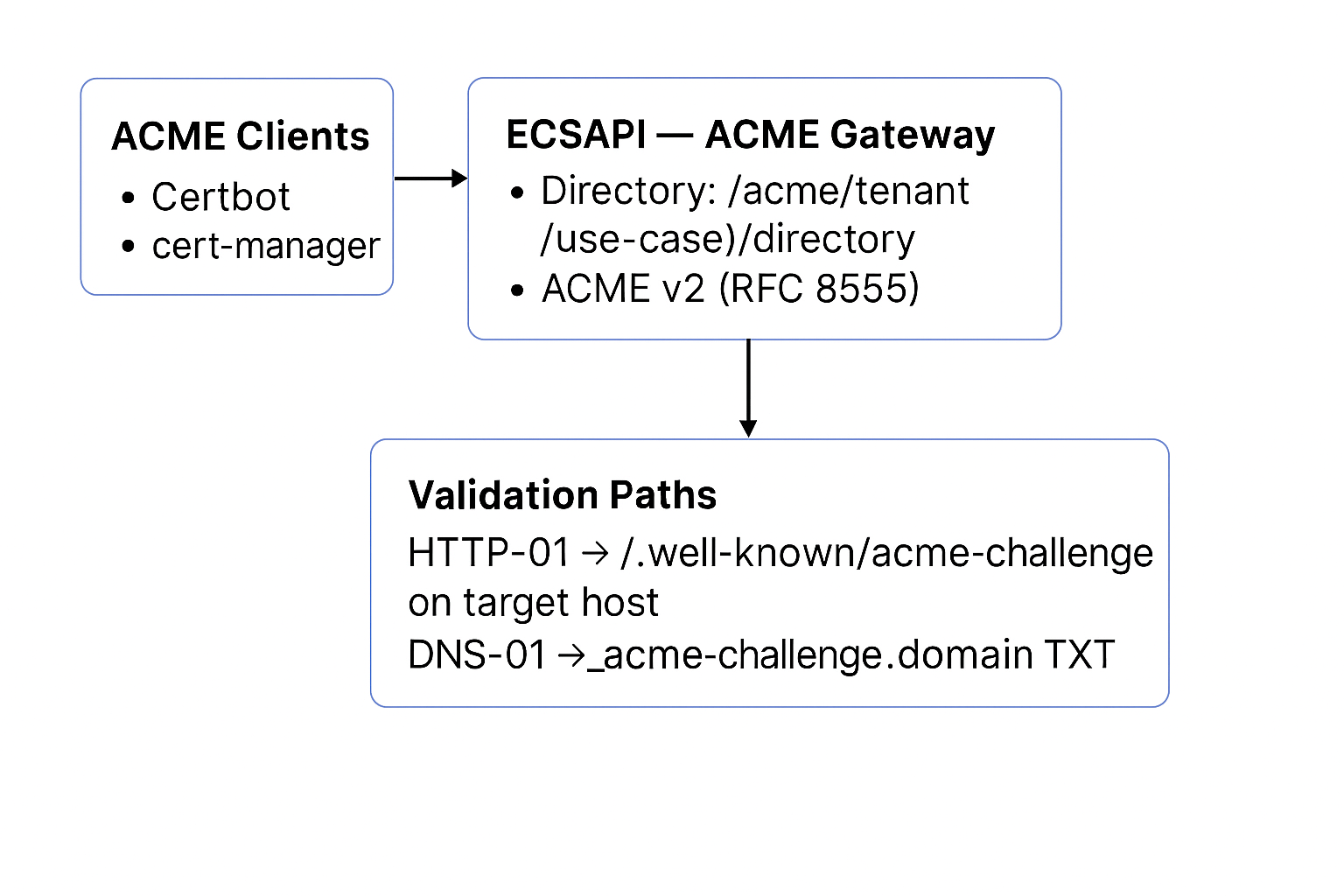
Certbot
Popular, well‑documented Python client. Works with HTTP‑01 or DNS‑01 for web based apps or servers
certbot certonly --server <DIRECTORY_URL> \
--manual --preferred-challenges http-01 -d example.com -d "*.example.com"
https://certbot.eff.org/certbot.eff.org
cert-manager (Kubernetes)
K8s controller that renews certs automatically using Issuer resources.
apiVersion: cert-manager.io/v1
kind: ClusterIssuer
metadata: { name: keyfactor-acme }
spec:
acme:
server: <DIRECTORY_URL>
externalAccountBinding:
keyID: <KID>
keySecretRef: { name: eab-secret, key: secret }
keyAlgorithm: HS256
privateKeySecretRef: { name: keyfactor-acme-account }
solvers:
- dns01: { route53: { region: us-east-1 } }
https://cert-manager.io/docs/configuration/acme/Docs